Email authentication through DKIM is no longer optional if you want your emails to reach inboxes consistently. A properly configured DKIM record helps mailbox providers verify that your messages are legitimate and haven’t been altered in transit. Without it, even genuine emails can end up in spam or get rejected altogether.
Email clients that successfully pass the DKIM check are more loyal to emails than to those that fail. At the same time, e-mail messages without DKIM headers are processed in standard mode.
In this guide, you’ll learn how to create a DKIM record, add it to DNS, test it correctly, and troubleshoot common issues.
What are the Benefits of DKIM?
A DKIM record plays a key role in proving that your emails are legitimate and haven’t been altered during transit. When DKIM is set up correctly, receiving mail servers can trust your messages more easily, which directly affects whether your emails land in the inbox, spam folder, or get rejected altogether.
How Does DKIM Improve Email Deliverability?
A cryptographic DKIM signature is applied to every outgoing email, allowing receiving servers to verify that the message came from your domain and wasn’t modified. This verification builds trust with mailbox providers, making them more likely to accept and deliver your emails to the inbox rather than filter them.
How Does DKIM Help Prevent Email Spoofing and Phishing?
By validating that an email was authorized by the sending domain, DKIM makes it harder for attackers to impersonate your brand. Even if someone tries to spoof your domain, their emails won’t pass DKIM checks, helping protect recipients from phishing attempts using fake or tampered messages.
DKIM Impact on Spam Filtering and Sender Reputation
Spam filters look closely at authentication signals like DKIM to judge sender credibility. Consistently passing DKIM checks tells mailbox providers that your domain sends reliable, well-authenticated email. Over time, this strengthens your sender reputation and reduces the chances of your emails being flagged as spam.
How to Create a DKIM Record For a Domain?
To create a DKIM record, first, list all your domains and sending services that are authorized to send emails on your behalf.
If you’re using ESPs (Email Service Providers) such as Google, Microsoft 365 and Third-Party services such as MailChimp, Sendgrid, etc. go to the given portal and create your DKIM record from there. Thus, these services store their DKIM Private Key in their servers. And provide DKIM Public Record to be stored in their users’ DNS Zones.
EasyDMARC has an in-built feature called Identified Email Sources. We identify more than 1,000 Email Sources. And provide recommendations for SPF & DKIM implementation redirecting to the source’s official documentation.
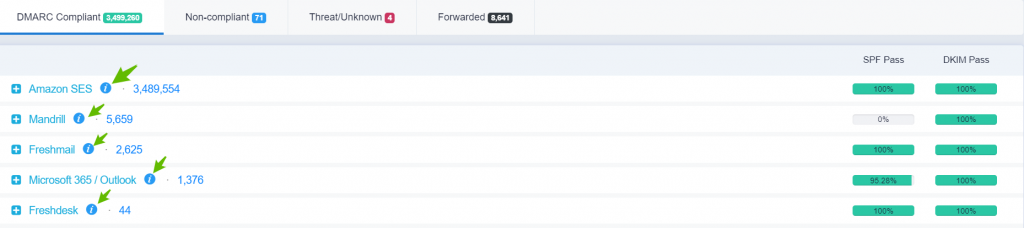
DMARC Aggregate dashboard, where you can see your outgoing mail stream from various sources (AmazonSES, Mandrill, etc.) that your organization uses.
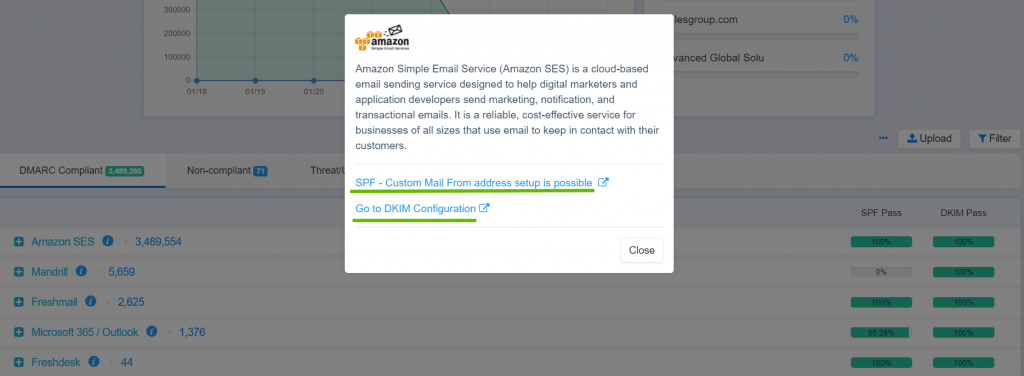
AmazonSES SPF & DKIM Configuration steps, by redirecting to their Official docs
If your organization has its own email server, it may have native DKIM functionality. Check the available documentation for the public/private key generation and policy record creation.
Most email service providers and tools like DKIM record generator simplify this process by creating the DKIM record for you, without manual key handling.
What Information is Needed to Generate a DKIM Record?
To understand how to create a DKIM record, you first need a few basic details: your domain name, a DKIM selector (used to identify the key), and the email service or sending platform you’re using. EasyDMARC automatically generates this information and provides a ready-to-publish DKIM record, reducing the risk of configuration errors.
How do DKIM Public and Private Keys Work?
DKIM uses a public–private key pair to sign and verify emails. The private key stays securely with your email server and signs outgoing messages. The public key is published in DNS as a DKIM record, allowing receiving servers to verify that the email hasn’t been altered.
Example of a DKIM Record
Here’s a clear example of a DKIM TXT record:
selector1._domainkey.example.com TXT “v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEArV9d1lZf9YQ3F2XzK9F8B9pQ2GfXqE9k8F6GZ8xYxQ5nH4WcZrZkYw9xJkKp8C5vQ2kL0rFqZ3QpP5cXK0M8FQIDAQAB”
Below is the breakdown of the elements of the example DKIM record:
- selector1- DKIM selector (can be anything like google, mail, dkim1)
- _domainkey.example.com- DKIM namespace for the domain
- v=DKIM1- DKIM version
- k=rsa- Key type
- p= – Public key used to verify email signatures
- _domainkey.example.com- DKIM namespace for the domain
How to Add a DKIM Record to DNS?
Once you know how to create a DKIM record, the next step is adding it to your domain’s DNS. This involves publishing the DKIM public key as a TXT record so receiving mail servers can verify your emails. While the steps are similar everywhere, the interface varies by DNS provider. Here are the general steps:
- Access the platform where your domain’s DNS is managed. This could be your domain registrar or a DNS service like Cloudflare or GoDaddy.
- Look for options such as DNS Settings, DNS Management, or Manage Zone for the domain you’re configuring.
- Choose TXT as the record type. In the Name/Host field, enter the DKIM selector provided by your email service (for example, selector1._domainkey).
- Copy the full DKIM public key value exactly as generated. Make sure there are no extra spaces, line breaks, or missing characters.
- Leave the TTL on default unless instructed otherwise, then save or publish the changes.
- DNS updates can take some time to apply. Once propagation is complete, you can verify the DKIM record using DKIM Record Lookup Tool.
Common DKIM DNS Mistakes to Avoid
Here are the frequent mistakes made when adding or managing DKIM records:
Incorrect DKIM record formatting
DKIM admins often copy the value incorrectly. Extra spaces, missing quotation marks, or broken public keys can prevent mail servers from reading the record, causing DKIM checks to fail even when everything else looks correct.
Using the wrong DKIM selector
A DKIM selector identifies which key should be used for verification. Using the wrong selector, or one that doesn’t match your email service configuration, means the receiving server can’t find the correct DKIM record, even though the record exists in DNS.
Creating duplicate DKIM TXT records
Adding multiple DKIM TXT records with the same selector is a common mistake. DNS should have only one DKIM record per selector. Duplicates confuse receiving servers and often result in failed DKIM or unpredictable authentication results.
Editing existing records instead of adding new ones
Another common issue is modifying an existing TXT record instead of creating a new DKIM entry. If you’re unsure what is a DKIM record and where it belongs, it’s easy to overwrite unrelated DNS records, which can break email authentication or other services.
How Long do DKIM DNS Changes Take to Propagate?
DKIM DNS changes are not instant. Depending on your DNS provider and TTL settings, propagation can take anywhere from a few minutes to 24–48 hours. During this time, DKIM checks may temporarily fail.
Can I Have Multiple DKIM TXT Records in a Single Domain?
A domain can have as many DKIM records for public keys as servers that send mail. Simply use different selector names.
DKIM selectors are part of DKIM Records, which allows the possibility of adding multiple DKIM Records in the given DNS Zone.
For example, if your organization uses Google Workspace & Sendgrid for the outgoing mail stream/strategies, then multiple DKIM Records can be added with different selectors.
For e.g
s1._domainkey.company.com IN TXT v=DKIM1; p=[Public Key] (where s1 is the selector for Sendgrid)
google._domainkey.company.com IN TXT v=DKIM1; p=[Public Key] (where google is the selector for Google Workspace)
How Can I Check My DKIM Record?
After you add a DKIM record to your DNS, it’s important to verify that it’s published correctly and actually working. A DKIM record that exists but isn’t properly configured won’t improve deliverability or authentication. Here is how you can check it manually and using online tools:
How to Manually Check a DKIM Record Using DNS Tools?
To manually check a DKIM record, you can use DNS lookup tools such as dig, nslookup, or web-based DNS checkers. Enter the full DKIM hostname, which includes the selector and _domainkey. If the DKIM record is set correctly, the lookup will return a TXT record containing v=DKIM1 and a public key. If nothing appears, the record may not exist, hasn’t propagated yet, or was added under the wrong name.
How to Test DKIM Using Online DKIM Checkers?
Online DKIM checkers are the easiest way to validate DKIM without touching command-line tools. You simply enter your domain and selector, and the tool checks whether the DKIM record is present, readable, and syntactically correct. Tools like DKIM checker also highlight common issues, such as formatting errors or missing selectors, making it easier to fix problems before they affect email delivery.
How to Confirm DKIM is Working in Email Headers?
The most reliable way to confirm DKIM is working is by inspecting email headers. Send a test email from your domain to an inbox you control, open the message headers, and look for a line that starts with DKIM-Signature or Authentication-Results. If DKIM is functioning properly, you’ll see a result like dkim=pass. If it shows ‘fail’ or ‘none’, the DKIM record may be missing, misconfigured, or not aligned with the sending domain.
Common DKIM Errors and How to Fix Them
Even after setting up DKIM, it’s common to run into the following errors that stop emails from authenticating properly:
DKIM Record Not Found
A “DKIM record not found” error means the receiving server can’t locate the DKIM TXT record in your DNS. This usually happens when the selector name is incorrect, the record was added under the wrong domain, or DNS changes haven’t fully propagated yet. Double-check that the selector in your email service matches the selector in DNS, and confirm the record exists using a DNS lookup or a DKIM checker.
DKIM Alignment Issues
DKIM alignment issues occur when the domain used to sign the email doesn’t align with the domain visible in the “From” address. While the DKIM signature may technically pass, misalignment can still cause DMARC failures. To fix this, ensure the DKIM d= domain matches or is a subdomain of the From domain, and update your email service settings if needed.
Invalid DKIM Signature Problems
An invalid DKIM signature means the email was altered after it was signed, or the public key in DNS doesn’t match the private key used by the sending server. This can happen if the DKIM record was edited, truncated, or copied incorrectly. Regenerating the DKIM keys and updating the DNS record usually resolves this issue quickly.
DKIM Records Made Simple: What to Do Next
Setting up DKIM correctly helps protect your domain, improve email deliverability, and reduce the risk of spoofing. From creating and adding a DKIM record to DNS, to testing and fixing common issues, each step builds trust with receiving mail servers. When combined with SPF and DMARC, DKIM becomes a strong defense against phishing and email abuse.
If you want an easier way to generate, publish, and monitor DKIM without DNS guesswork, start a free EasyDMARC trial to validate your DKIM setup, spot issues early, and keep your email authentication on track.
Frequently Asked Questions
Yes, DKIM works independently and can authenticate emails on its own. However, combining DKIM with SPF and DMARC provides stronger protection, better deliverability, and clearer enforcement against spoofing.
DKIM keys should ideally be rotated every 6–12 months. Regular rotation limits exposure if a key is compromised and aligns with email security best practices.
Yes, both Google and Microsoft strongly recommend DKIM. Proper DKIM setup is essential for bulk senders and helps prevent spam filtering and delivery issues.