DMARC Made Simple
Your one-stop solution for all things DMARC. Solve email security and deliverability issues in just a few clicks.
Join the 175,000+ domains secured with us
Simplify, Manage, and Automate Your DMARC Journey: EasyDMARC It
Protect your company reputation, ensure compliance with industry regulations, and boost email deliverability with our DMARC platform.
Reliable
Trusted by over 175,000 domains, we deliver robust, scalable solutions that grow with your organization’s needs, ensuring long-term security and stability.
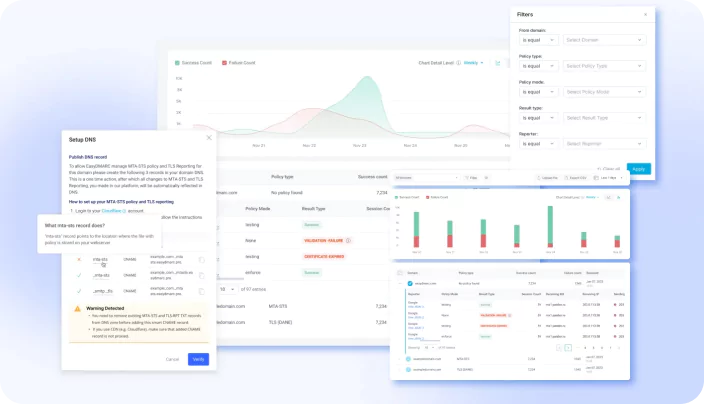
Easy to Manage
Our smart dashboards and simplified reporting keep your email authentication on track, reducing time spent troubleshooting and increasing operational efficiency.
Risk-Free
We provide peace of mind with world-class support, available 24/7, so you can focus on your business while we handle your email security.
Fast
Our streamlined DMARC implementation ensures a rapid, hassle-free transition from monitoring to full enforcement, minimizing disruptions and enhancing email deliverability.
Key Features for Enhanced Security and Deliverability
Reduce cyberattack risks, solve deliverability issues, and manage your domain quickly and reliably with our easy-to-use platform.
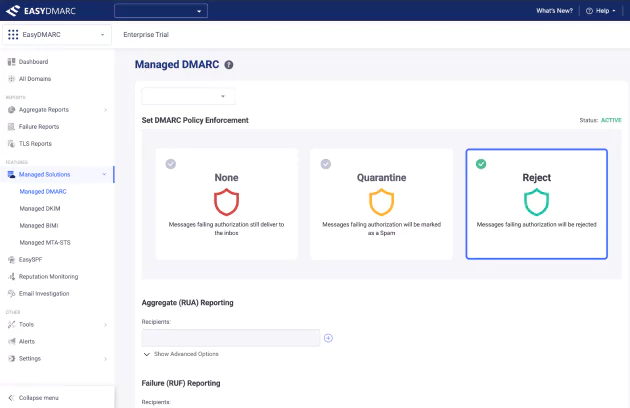
Managed Services
Our white-glove solution provides a safe and comprehensive setup and management of DMARC, SPF, and DKIM. From configuration to enforcement, our experts ensure your email authentication is accurate, secure, and aligned with best practices. A dedicated DMARC Engineer supports you every step of the way.
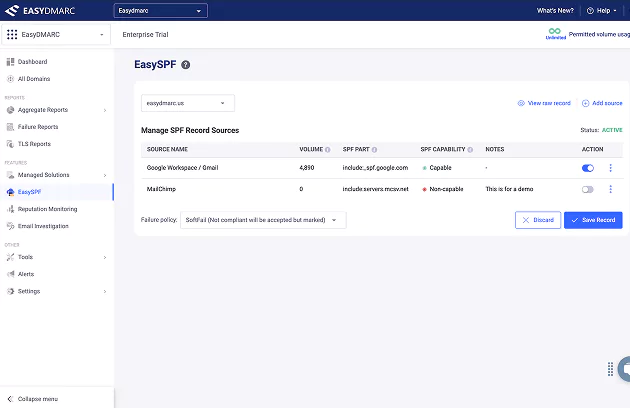
Find Out MoreEasySPF
EasySPF simplifies SPF setup and management with a one-time DNS configuration. Manage your SPF record from a centralized platform and automatically update it to reflect any changes. EasySPF eliminates issues like the 10 DNS lookup limit by dynamically flattening the record, converting domain includes into IP addresses.
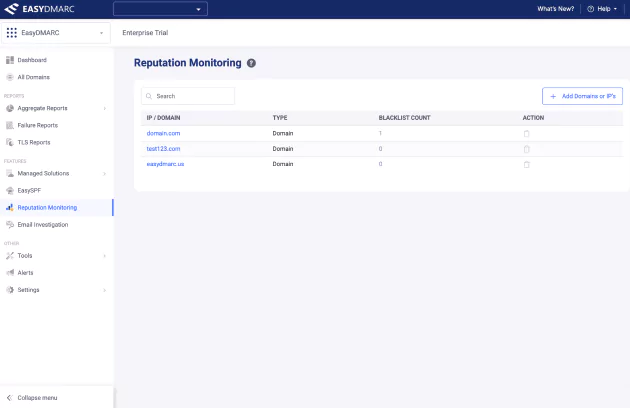
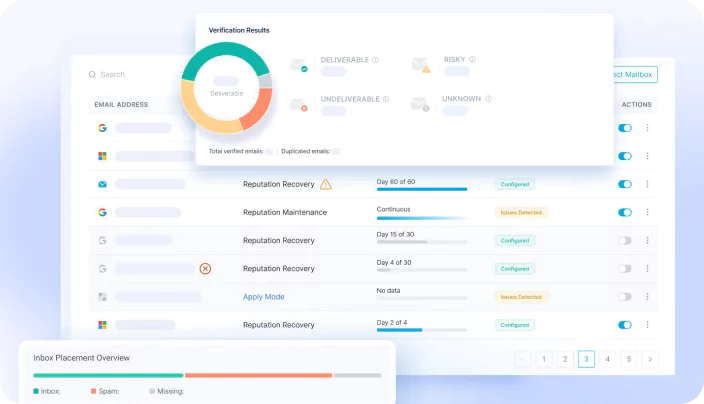
Start ExploringReputation Monitoring
EasyDMARC's Reputation Monitoring helps you stay ahead of potential email deliverability issues by tracking your domains and IP addresses against blacklists. With real-time automated checks and email alerts, you’re immediately notified if your domain or IP appears on a blacklist. With direct links to blacklist sites, you can quickly delist it.
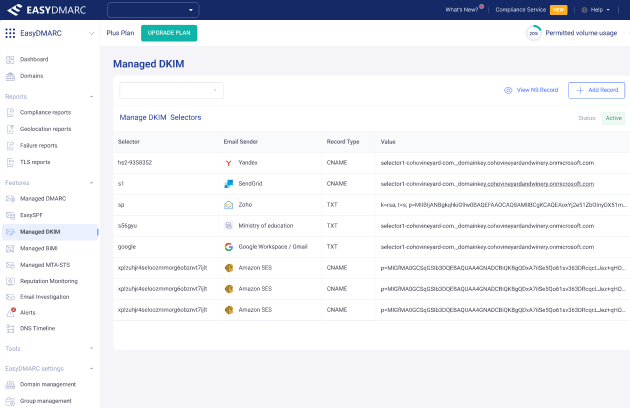
Find out MoreManaged DKIM
Managed DKIM simplifies email authentication by centralizing DKIM record management for multiple domains. It automates selector detection and reduces manual setup, minimizing errors and improving deliverability. With an easy-to-use interface, Managed DKIM ensures seamless management of DKIM selectors across multiple domains.
Get in TouchDMARC Compliance Made Easy
DMARC is mandatory in many industries globally, as protecting company data and consumer privacy becomes increasingly important. Your business needs to become compliant with regulations quickly, accurately, and without risk, and EasyDMARC makes compliance seamless.
Here are some of the regulations that mandate DMARC compliance as best practice in email security:
| REGULATION | WHAT IT MEANS | REGION | INDUSTRY |
|---|---|---|---|
| Microsoft sender requirements | Requirement to set up SPF, DKIM, and DMARC for sending domains | Global requirement from 5 May 2025 | All companies sending over 5,000 emails daily that include hotmail.com, live.com, and outlook.com consumer domain addresses |
| Google & Yahoo sender requirements | Requirement to set up SPF, DKIM, and DMARC for sending domains | Global requirement from February 2024 | All companies sending over 5,000 emails daily that include Google or Yahoo addresses |
| General Data Protection Regulation (GDPR) | Europe’s primary data privacy and security law | EU countries | All industries |
| Digital Operational Resilience Act (DORA) | Framework to manage ICT cybersecurity risks | EU countries from January 2025 | Financial institutions (insurers, banks, lenders, financial and investment advisors) |
| Network and Information Security Directive (NIS 2) | Revised EU Directive on ICT cybersecurity risks | EU countries from October 2024 | Multiple sectors, including telecoms, ICT, health, energy, chemicals, and manufacturing |
| Payment Card Industry Data Security Standard (PCI DSS 4.0) | Technical and operational requirements to protect payment data | Global requirement from March 2025 | All companies processing, storing, or transmitting payment card data |
| California Consumer Privacy Act (CPPA) | Provides privacy rights and consumer protection | All companies targeting people in California, US | All industries |
| The Gramm-Leach-Bliley Act (GLBA) | Safeguards consumers' financial information and requires transparency in how it's shared | US | Financial institutions (insurers, banks, lenders, financial and investment advisors) |
| The Health Insurance Portability and Accountability Act (HIPAA) | Establishes standards to protect personal health information | US | Healthcare industry |
EasyDMARC Blog. Enrich Your Email Security Knowledge
Get the email security content, DMARC, SPF, DKIM, and BIMI technical knowledge, and cybersecurity-related articles from our DMARC engineers.
WE’RE FEATURED IN








Guard Against Financial, Data, and Customer Loss
Use EasyDMARC to prevent cybercriminals from sending fraudulent emails to your business partners, employees, and customers from your business email addresses.
WE BLOCK
380K+
DOMAIN SPOOFING ATTEMPTS
PER DAY
WE AUTHENTICATE
9B+
EMAILS
PER DAY
WE ANALYZE
27M+
DATA POINTS
PER DAY
WE SEND
180K+
DMARC REPORTS
PER WEEK
WE CHECK
15K+
PHISHING URLS
PER WEEK
WE MONITOR
14K+
DOMAINS
PER WEEK
175,000+ domains from 130 countries
Global presence
4 OfficesUS, UK, Netherlands & Armenia
Great companies meet and beat compliance with EasyDMARC
Discover shared thoughts and learn more about businesses growing safely with EasyDMARC.
Start Your DMARC Journey
With Our Free Courses
EasyDMARC Academy is a free, self-paced learning platform built to make email authentication easier to understand for everyone, from beginners to IT professionals. Our courses break down complex topics like SPF, DKIM, and DMARC into clear, practical lessons that help you protect your domain from phishing, spoofing, and other email-based threats.
Whether you're just starting out in cybersecurity or are an experienced IT specialist, the Academy offers free, accessible certification programs designed to boost your expertise. As you complete each course, you'll earn recognized certifications that enhance your professional credibility and open up new career opportunities.
Enroll Now