EasyDMARC Support is always ready to help. Companies of all sizes deploy DMARC. They use our tools and keep their domain secure.
DMARC deployment can be managed just like any other project.
DMARC deployment process is very easy. It has NO risks. The lightweight project can be used to install DMARC at any organization.
EasyDMARC Support helps to work quickly and efficiently.
What we do
- We help to create and run the one-time deployment project.
- The project installs the necessary processes within an organization to ensure DMARC-compliance. DMARC gets back into daily operations.
- We allow a sender’s domain to indicate protected emails by SPF and/or DKIM, and tell a receiver what to do if neither of these authentication methods pass (e.g. junk or reject the message).
We continue maintaining and managing DMARC compliance even when the project is over, similar to how DNS and SSL certificates are managed.
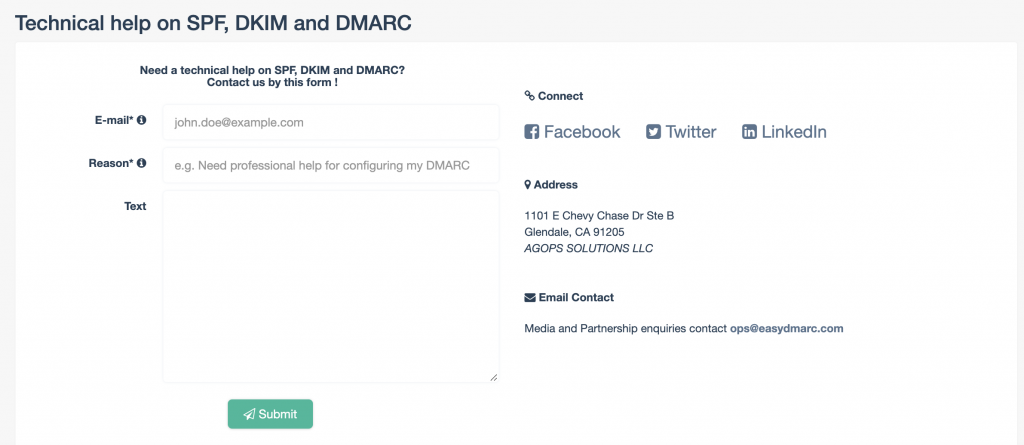
Contact us if you need a good partner!





Hello,
Let me clarify that I am not a technical expert, or barely any knowledge of DMARC stuff.
My name is Hassan and I want to talk about a problem I have had for the past 2 months with setting my DKIM record value for my domain resolveresults.com over at Namecheap.
Let me quickly clarify that I have set up my DKIM record with the DKIM record my email provider Zoho mail has provided me.
I used EASYDMARC’s generator tools to generate my spf, dmarc, and dkim record values which went well for spf and dmarc, except for dkim ( was a total disaster ).
Generating the keys wasn’t the problem, however when I would copy paste the values given to me by the tool, it would say selector invalid.
I used mail tester and it would say my DKIM record was invalid and I made sure that the values were correct, but still I was facing trouble.
I generated many, probably 8 DKIM records to try and get this to work, but I had zero luck.
Then I thought that I probably have to copy paste the values host and value inside my email providers records then do it for my domain. However, I can’t seem to add my own DKIM ( the generated one from EASYDMARC ) to my email provider. I don’t know if that means DKIM for me is useless, or that I have to do something else.
I’m currently using what Zoho has provided me, but does that mean I can’t use the DKIM tool for my mail, nor my domain?
Thank you for taking your time to read this
Hassan
Hey Hassan,
If you’re using an ESP to send out emails (in your case, I guess Zoho?), you’ll need to get the public key directly from Zoho’s portal. Since ESPs keep the private keys in their backend and only provide the public key to their customers, you can’t use EasyDMARC’s DKIM generator tool to generate keys for your ESP.
Our DKIM generator tool is specifically designed for dedicated servers, not for ESPs or third-party senders like Google Workspace, Microsoft 365, Zoho Mail, Mailchimp, etc.
You can also check out our article on how to get DKIM for your Zoho Mail: Zoho Mail SPF and DKIM Setup.