This instructional article will demonstrate the Mimecast configuration process of Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM) Signatures to ensure Mimecast passes the DMARC alignment check and eliminates spam from your domain and increases security.
The SPF record identifies the mail servers and domains that are allowed to send email on behalf of your domain. The DKIM record, on the other hand, is a specially formatted DNS TXT record that stores the public key the receiving mail server will use to verify a message’s signature. These email authentication methods will be used to prove to ISPs and mail services that senders are truly authorized to send email from a particular domain and are a way of verifying your email sending server is sending emails through your domain.
The process of setting up the SPF record
To ensure the emails from Mimecast are sent on behalf of your domain, we need to create or update your existing SPF record by including the following information.
| Field / Option | Description |
| Europe (excluding Germany) | include:eu._netblocks.mimecast.com |
| Germany | include:de._netblocks.mimecast.com |
| United States of America | include:us._netblocks.mimecast.com |
| Canada | include:ca._netblocks.mimecast.com |
| South Africa | include:za._netblocks.mimecast.com |
| Australia | include:au._netblocks.mimecast.com |
| Offshore | include:je._netblocks.mimecast.com |
| Global (includes all the above) | include:_netblocks.mimecast.com |
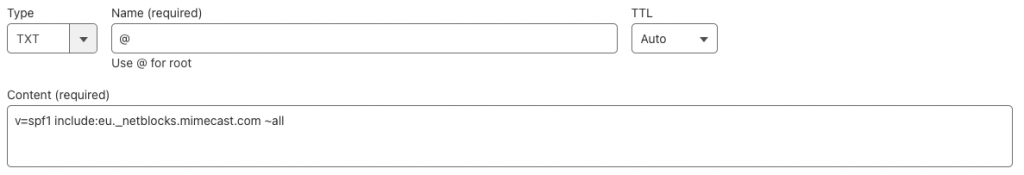
As listed in the information above, check your server location and add the Include: mechanism in your SPF Record. For this example, we’ll be using the Europe option.
- Copy the provided SPF record and navigate to your DNS provider (CloudFlare, Godaddy, etc.) and create a TXT Record. We’ll be using CloudFlare for this example.
- Click on “Save”
- Wait up to 72 hours to allow your DNS to process the changes
Important Note: Each domain must have only one SPF TXT Record. If you have multiple SPF Records, SPF will return a PermError.
If you are using multiple IPs, ESPs, Third-Party services for your various email strategies, you should include them in a single SPF Record.
E.g v=spf1 ip4:18.57.156.221 include:eu._netblocks.mimecast.com include:thirdpartyservice.com ~all
(Use our free SPF testing tool to test your SPF records.)
The process of setting up the DKIM record
To ensure the emails from Mimecast are sent on behalf of your domain, we need to create a new DKIM record using the following information.
- Login to your Mimecast account
- Navigate to the Administration dropdown menu, and on the menu select Gateway > Policies
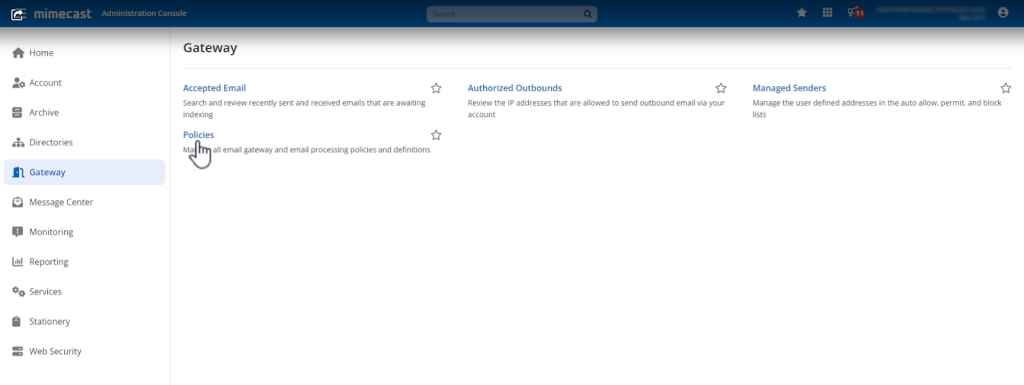
- In the Policies page, click on Definitions, and from the dropdown menu select DNS Authentication – Outbound

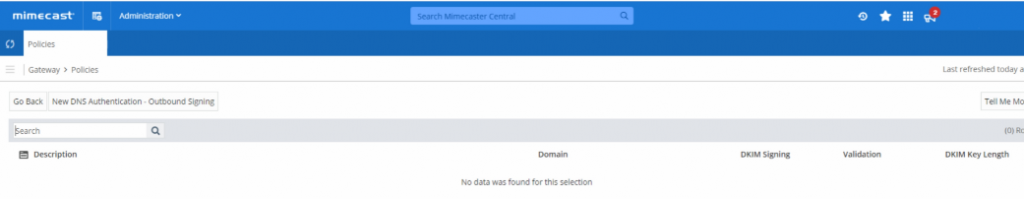
- Now to create a new DKIM policy, click on New DNS Authentication – Outbound Signing
- You need to fill in the description box, select the domain from the lookup list for which you want to setup DKIM, and name your DKIM selector
- In the DKIM length category, you can select either 1024 bits or 2048 bits if you want more secure encryption. Then click Generate.
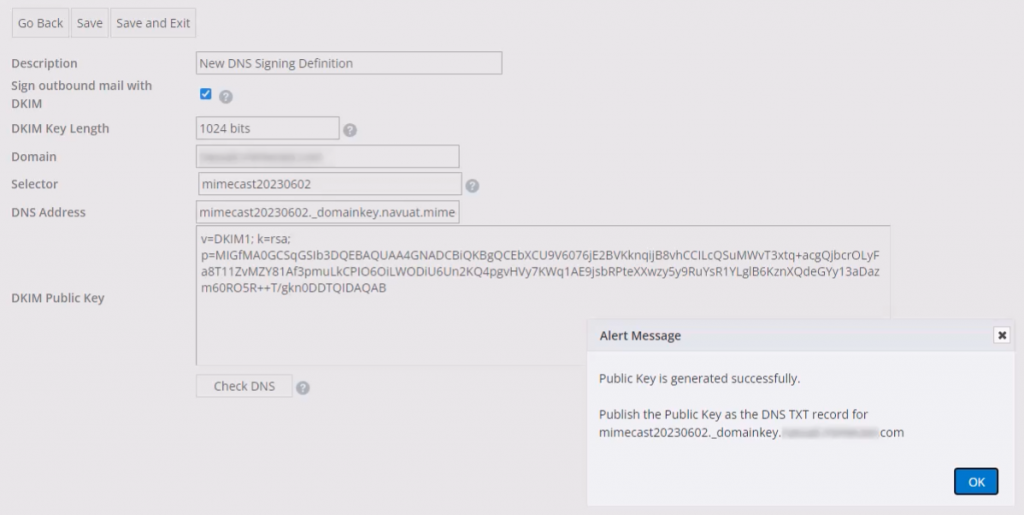
- Once done, click on Save and Exit
IMPORTANT NOTE: Your DKIM public key will be generated successfully for Mimecast. Now you can simply go to your DNS registrar and publish the DKIM key in your domain’s DNS for hostname: selector._domainkey.yourdomainname.com
- Once done with your outbound signing definition, next you need to create your outbound policy.
The process of setting up the Outbound policy
- For this go to Policies > DNS Authentication – Outbound
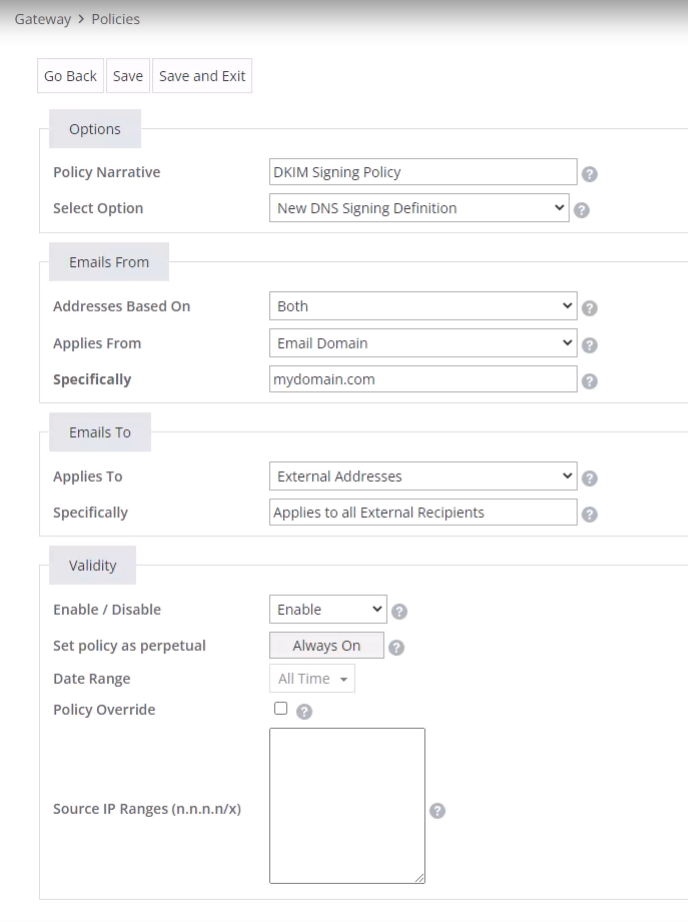
- You need to add a new DKIM policy for your outbound signing with values as shown below:
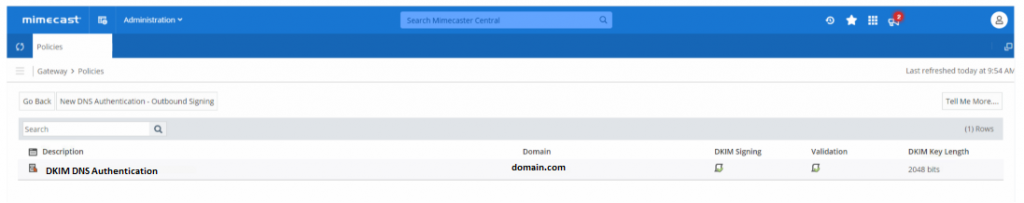
- In order to verify that your DNS has been added to your hosting environment, click on save and exit and then check DNS in your Mimecast account.
- Make sure you get a verified status for both DKIM Signing and Validation, and you are done.
Congratulations, you now successfully authenticated your outgoing mail stream from Mimecast with SPF and DKIM.
Important note: If the provider recommends publishing also a DMARC record, there’s no need to do so if you already have a DMARC record in place, as each domain can only have one DMARC record.






Thanks