Email remains one of the most targeted channels for spoofing and phishing, making proper authentication essential for protecting your domain and maintaining consistent deliverability. Without proper controls in place, unauthorized senders can impersonate your brand, damage your reputation, and reduce inbox placement across major email providers.
To address this, organizations rely on email authentication service providers that help manage authentication records, monitor sending activity, and provide visibility into how emails are being validated. Instead of manually handling DNS configurations and raw reports, these platforms make it easier to understand who is sending on your behalf and whether those messages are properly authenticated.
What Email Authentication Services Actually Do
Email authentication services help organizations implement and monitor systems that verify whether messages pass authentication checks and are associated with authorized sending sources. Instead of relying on manual DNS management and fragmented data, these platforms centralize authentication insights and make it easier to maintain control over your domain.A reliable email authentication service helps organizations identify and control which senders are authorized to use their domain through authentication and DMARC policy enforcement.
Core authentication protocols every provider should support
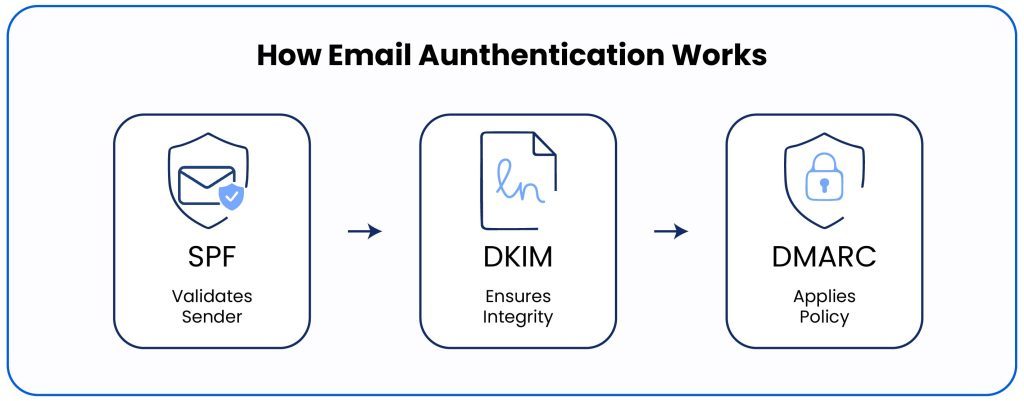
At the foundation of any authentication setup are three essential standards: SPF, DKIM, and DMARC. Together, they validate sending infrastructure, confirm message integrity, and define how receiving servers should handle unauthenticated emails.
A strong provider must fully support these protocols and help organizations configure them correctly. These email authentication protocols work together to establish trust between sending and receiving servers, reducing the risk of spoofing and improving overall deliverability.
Monitoring authentication results and sending sources
Beyond setup, authentication services continuously analyze DMARC reports to provide visibility into email activity across your domain. These reports show which services are sending emails, whether authentication checks pass or fail, and where potential risks exist.
By translating complex reporting data into clear insights, providers help organizations identify unknown sending sources, fix authentication issues, and maintain an accurate inventory of all legitimate email services.
Key Features to Look for in an Email Authentication Service Provider
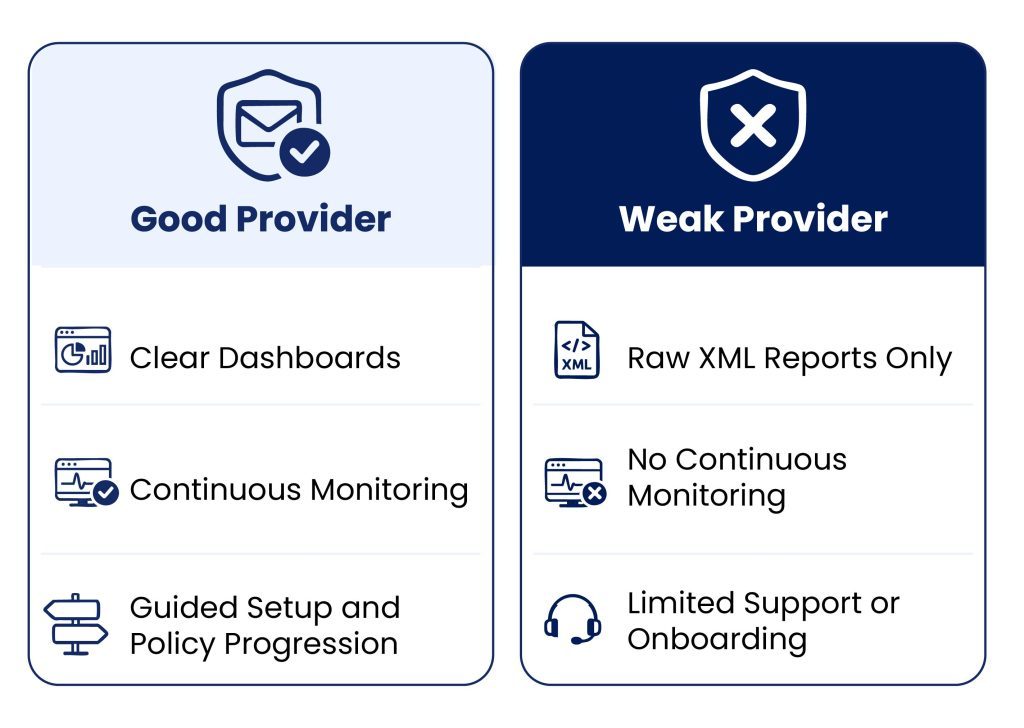
Reliable providers go beyond basic setup. They offer tools that simplify authentication deployment while giving teams continuous visibility into sending activity and authentication performance.
Clear visibility into DMARC reports
DMARC reports are highly detailed but often difficult to interpret in raw XML format. A strong provider translates this data into intuitive dashboards that highlight authentication success rates, sending sources, and potential spoofing attempts.
Tools like a DMARC checker help teams quickly assess domain status and identify issues without digging through complex reports, making it easier to act on authentication insights.
Tools to validate and troubleshoot authentication records
Authentication depends heavily on correct DNS configuration. Even small errors in SPF or DKIM records can lead to failures that impact deliverability.
A reliable provider includes diagnostic tools such as an SPF Lookup, allowing teams to verify records, detect misconfigurations, and troubleshoot issues before they affect email performance.
Guided policy progression
Moving directly to strict DMARC policies without proper visibility can disrupt legitimate email flows. Strong providers guide organizations through a gradual progression, starting from monitoring mode and moving toward quarantine or reject policies once all sending sources are validated. This structured approach reduces risk while improving enforcement over time.
EasyDMARC, for example, helps guide this process by providing visibility into authenticated sources and reducing the risk of enforcing policies too early.
Domain and sender discovery
Organizations often use multiple platforms to send emails, including marketing tools, CRMs, and internal systems. Not all of these sources are always documented.
Authentication providers help identify and map all legitimate sending services associated with a domain. This ensures that a valid email is not unintentionally blocked while unauthorized sources are detected and addressed.
Red Flags When Evaluating Email Authentication Providers
Not all providers offer the same level of visibility, support, or reliability. While many tools claim to simplify authentication, some fall short when it comes to monitoring, usability, and long-term management.
Limited reporting visibility
Providers that only display raw DMARC reports or offer minimal dashboards make it difficult to understand what is actually happening across your domain. Without clear insights into authentication failures and sending sources, teams may miss misconfigurations or unauthorized activity.
Lack of monitoring or alerting
Email environments change constantly as new tools and services are introduced. If a provider does not offer continuous monitoring or timely alerts, authentication issues can go unnoticed for long periods, increasing the risk of spoofing or deliverability problems.
Poor documentation or onboarding support
Setting up authentication often requires DNS updates and coordination across multiple systems. Providers that lack clear documentation or are guided onboarding can slow down implementation and increase the likelihood of configuration errors.
Confusing pricing tied to sending volume
Authentication services are primarily focused on domain monitoring and reporting, not email delivery. Providers that base pricing heavily on sending volume can create unnecessary costs and confusion, especially for organizations managing multiple domains or platforms.
Questions to Ask Before Choosing an Email Authentication Provider
Evaluating a provider is not just about features. It also involves understanding how well the platform supports ongoing monitoring, troubleshooting, and policy enforcement. Asking the right questions helps uncover whether a provider can handle real-world authentication challenges.
How do you monitor authentication failures and spoofing attempts?
A reliable provider should offer continuous monitoring of authentication results across all sending sources. This includes identifying failed SPF or DKIM checks, detecting unusual sending patterns, and surfacing potential spoofing attempts based on reporting data.
What reporting tools do you provide for DMARC insights?
Look for platforms that transform DMARC data into actionable insights. Instead of raw reports, providers should offer clear dashboards, filtering options, and trend analysis to help teams understand authentication performance and quickly investigate issues.
Do you provide tools to validate SPF and DKIM records?
Since authentication relies on accurate DNS records, providers should include built-in tools that allow teams to verify SPF and DKIM configurations. This helps prevent misconfigurations and ensures that all legitimate sending services are properly authorized.
How do you help organizations safely move to DMARC enforcement?
Moving to stricter DMARC policies requires careful planning. Strong providers guide organizations through a phased approach, helping validate sending sources, monitor results, and reduce the risk of blocking legitimate email before enforcing quarantine or rejection policies.
How Email Authentication Services Help Reduce Spoofing Risk
Email authentication services play a critical role in protecting domains from unauthorized use. By validating sending sources and enforcing authentication policies, these platforms help organizations identify suspicious activity and reduce the risk of fraudulent emails reaching recipients. Enterprise-focused email authentication platforms like EasyDMARC support this by combining continuous monitoring, sender visibility, and guided policy enforcement.
Through continuous monitoring and analysis of authentication results, providers can identify unknown or unauthorized senders attempting to use your domain. This visibility allows teams to investigate and take action early, whether by updating authentication records or enforcing stricter policies.
As organizations strengthen their authentication setup, they are better equipped to prevent spoofing and protect both their brand and their recipients from phishing and impersonation attacks.
Choosing the Right Email Authentication Service
Choosing the right provider comes down to more than just protocol support. The most reliable solutions combine strong authentication coverage, clear reporting, and continuous monitoring, helping organizations maintain full visibility into their email ecosystem.
A well-designed email authentication service simplifies complex processes like DNS configuration, report analysis, and policy enforcement, while guiding teams through each stage of authentication maturity. This reduces operational overhead and minimizes the risk of misconfigurations.
Ultimately, organizations should prioritize providers that offer clarity, control, and ongoing support. With the right platform in place, managing authentication becomes a structured, scalable process rather than a reactive effort.
FAQ
An email authentication service provider helps organizations set up, manage, and monitor authentication protocols like SPF, DKIM, and DMARC. These platforms centralize authentication data, making it easier to track sending sources, identify failures, and maintain control over who can send emails on behalf of your domain. They also simplify complex reporting and support ongoing enforcement.
SPF, DKIM, and DMARC work together to verify that emails are sent from authorized sources and have not been altered in transit. SPF validates sending servers, DKIM ensures message integrity, and DMARC defines how to handle failed authentication. Together, they reduce spoofing risks and improve trust with receiving mail servers.
DMARC reports provide detailed insights into who is sending emails on behalf of your domain and whether those messages pass authentication checks. By analyzing this data, organizations can identify unauthorized senders, identify suspicious activity, and take corrective action before spoofing attempts impact recipients or brand reputation.
Most authentication platforms include tools that help verify DNS records and detect configuration issues. These tools can check SPF, DKIM, and DMARC setups to ensure they are correctly implemented and aligned with your sending infrastructure. This helps prevent authentication failures that could affect deliverability.
The initial setup of SPF, DKIM, and DMARC can take a few hours to a few days, depending on the complexity of your email environment. However, full implementation, including monitoring and policy enforcement, is an ongoing process. Organizations typically spend several weeks analyzing reports and validating sending sources before moving to stricter enforcement policies.