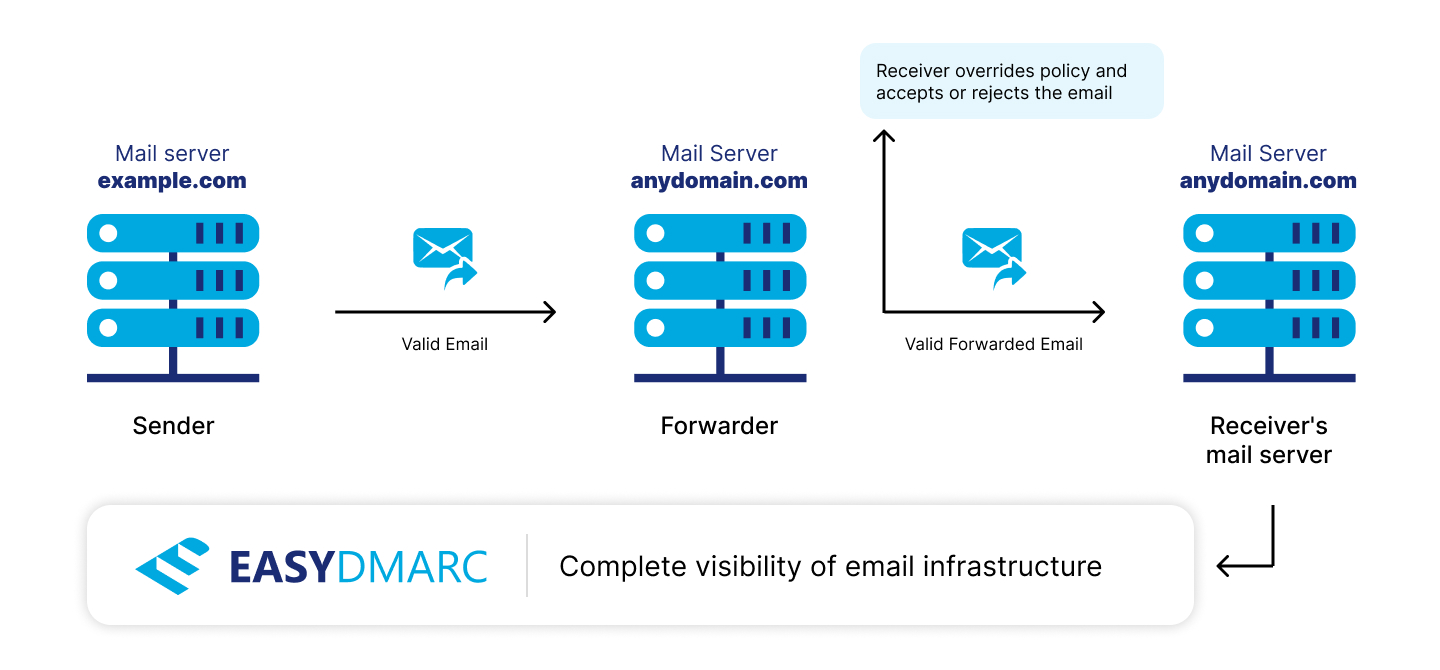
When analyzing DMARC Aggregate reports, you may come across Policy Overrides, listed on the “Forwarded” tab. In most cases, the recipient server will apply the DMARC-Record-Specified Policy on your domain. But there may be exceptions, where DMARC Policy Override occurs.
So, let’s break this into 2 different cases, where Policy Override occurs:
Case 1: When you have an enforced DMARC Policy (p=quarantine or p=reject) and your outgoing email goes through a mailing list which breaks SPF and DKIM Authentication checks
Case 2: Due to modification of the content and structure of original email, DKIM signature integrity broke on the way to the final destination
In these two given cases, DMARC will Fail but the recipient server identifies it as either legitimate or sure forwarder, thus overriding applied DMARC Policy and accepting the email.
DMARC Policy Override examples
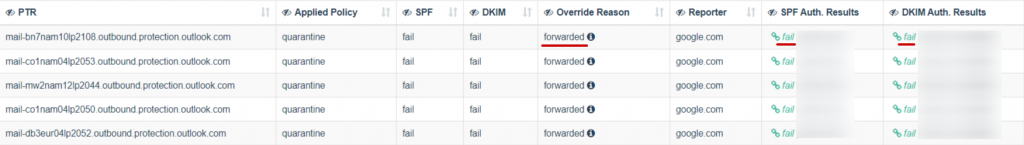
Here are the screenshots of well-known DMARC Policy overrides that you may encounter in your EasyDMARC dashboard:
1- Local_policy
2- Forwarded
Some of the common DMARC Policy overrides are described below:
- Forwarded: Message was relayed via a known forwarder, or local heuristics identified the message as likely having been forwarded. There is no expectation that authentication would pass.
- Local_policy: The Mail Receiver’s local policy exempted the message from being subjected to the Domain Owner’s requested policy action.
- Mailing_list: Local heuristics determined that the message arrived via a mailing list, and thus authentication of the original message was not expected to succeed.
- Other: Some policy exceptions not covered by the other entries in this list occurred.
- Sampled_out: Message was exempted from the application of policy by the “pct” setting in the DMARC policy record.
- Trusted_forwarder: Message authentication failure was anticipated by other evidence linking the message to a locally-maintained list of known and trusted forwarders.
Descriptions of the PolicyOverrideTypes listed on RFC 7489
Sign Up to automatically process and analyze your DMARC reports.