Email security breaches cost billions of dollars every year, ranging from $50k per attack for small businesses and $3.86m for each phishing attack mid size businesses. And because security breaches are growing by 11% each year, businesses are turning to Domain-based Message Authentication, Reporting & Conformance (DMARC) to help stem the tide. But, how can you start using it to save your business money and grow client trust? In this ultimate guide we’re walking you through everything you need to know about DMARC, including what it is, how it helps you protect your business and your clients, and how you can implement DMARC.
What Is DMARC?
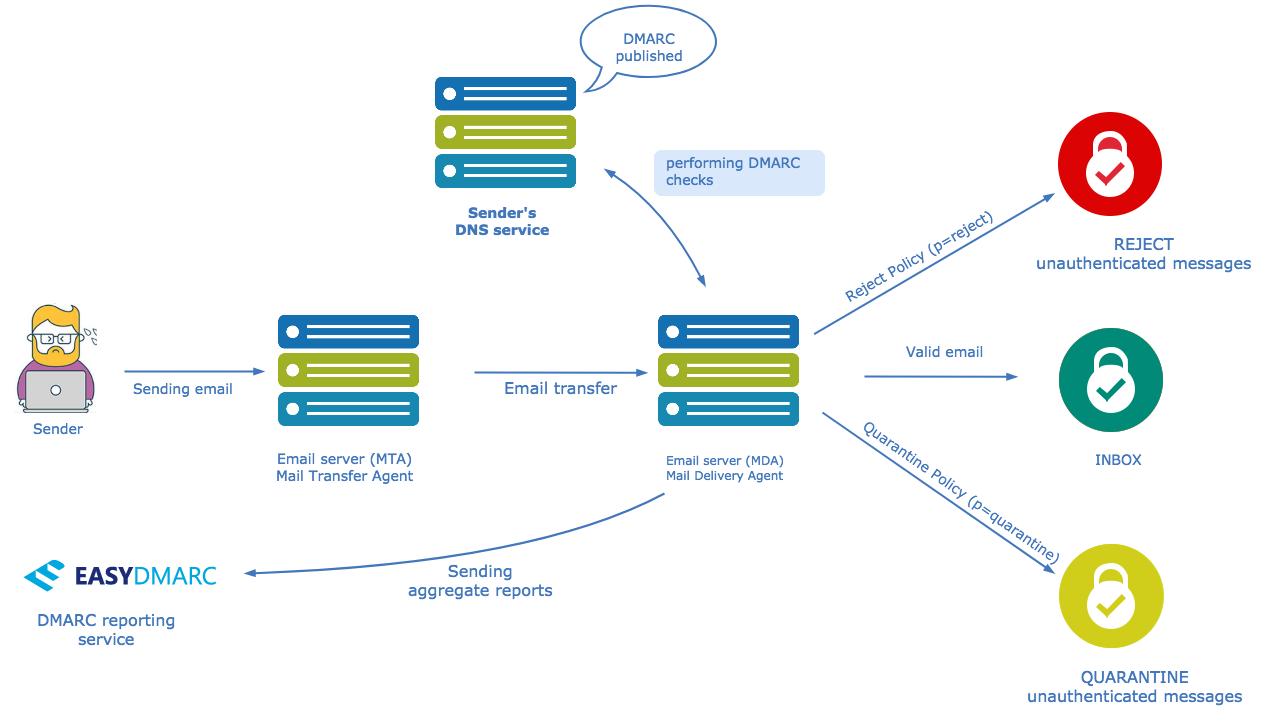
Simply put, DMARC is an email authentication strategy that cuts down on fraudulent emails. It takes Sender Policy Framework (SPF) and Domain Keys Identified Mail (DKIM) standards to the next level by ensuring that emails reach those standards before letting them through. As a result, legitimate emails are passed through, and fraudulent emails, or emails that appear to come from your domain but actually came from an unscrupulous individual, will be blocked.
DMARC primarily works to ensure that the “from” field (sender address) setting in the header is consistent in two ways.
First, it uses SPF to make sure that the domain matches in both “header from” and the “Return-Path”
Second, it makes sure that the domain mentioned in the “header from” matches the “d=domain name” in the DKIM signature.
If both of them do not match, emails will not be cleared for the inbox. Furthermore, you can set up a robust DMARC policy that tells receiving email providers how to handle your mails. Ultimately there are three options:
- Accept all mails regardless of DMARC lookup has passed or failed
- Push failed mails to Spam
- Reject failed mails entirely
What Problems Does DMARC Solve?
Ultimately, DMARC reduces the amount of spam or fraudulent emails that may arrive at YOUR CUSTOMERS inboxes that look like they came from you.
Thus, by protecting your domain with DMARC you essentially protect your company brand and reputation.
What Problems Does DMARC Not Solve?
The most common misconception about DMARC is that it will reduce the amount of spam you receive in your mailbox. This is not really correct.
In fact, DMARC will reduce the amount of spoofed / fraudulent mails, sent on behalf of you, that your customers may receive.
To reduce your inbound spam you need to have a good and properly configured Spam detection system.
DMARC doesn’t stop all kinds of phishing attacks, so users will always need to be wary of requests for personal information. Most reputable companies won’t contact you via email to ask for things like credit card details, bank information, passwords, or social security numbers. And, a DMARC protocol will prevent spoofing of domains you trust like “mybank.com.”
However, where a lot of phishing attacks find success is in “look-a-like” domains. Using the example above, they might not send it from “mybank.com,” but might send from “mybank.us” or “mybanks.com” or domains that look a lot like the domain you’re expecting the email to be from. Spammers are often sophisticated and spoof the normal message signatures, so the email looks almost identical to one from the real company.
Another common practice for these fraudulent emails is to direct you to a link at a spoofed website. At the “looks like” domain where you may pay a fraudulent invoice, give them a password, or enter other personal information.
As a result, consumers will always need to be aware of potentially problematic emails. And instead of replying to that email to confirm legitimacy, they should look up the real phone number online and call their contact directly.
Why You Need DMARC
When fraudulent emails make it to customer inboxes, there are all kinds of inherent dangers, from identity theft to outright theft of money or other information. This is particularly troubling when the emails appear to come from someone trustworthy, whether your bank, the IRS, or even a business partner.
The chief benefits boil down to:
- Brands can let everyone know they are following good email authentication practices, which builds trust with your clients, but also creates a red flag to would-be fraudsters that your brand is more difficult to spoof and they should move on to easier targets.
- Domain owners are able to receive feedback about addresses using their domain to send email.
- Brands can set guidelines for what will happen to emails that do not pass muster.
- Consumers can have confidence that the person sending the email from your brand is who they say they are.
Basically, you can think of DMARC as the ultimate traffic cop for your customers inboxes. DMARC’s main goal is to make sure that people are following your rules.
Myths About DMARC
Now that we’ve laid out what DMARC is and why you need it, it’s time to dispel some of the top DMARC myths.
Myth #1: DMARC Blocks All Email Attacks
Although we briefly explained this in the section above “What does DMARC not solve?” we can go into more of the specifics here. A well-configured DMARC protocol will ensure that email receivers can tell whether an email came from the actual person at your domain sending it, or whether it was sent by someone with ill intentions.
The important words here are “at your domain.” It helps protect consumers from emails that are spoofed. In other words, their email service provider will be able to detect that the emails were spoofed, and although they appear to originate from your domain, they are fraudulent.
DMARC, however, does not protect against “look alike” phishing schemes. There’s a big difference here. If an email from [email protected] is sent by a fraudster and you have a properly configured DMARC protocol in place, the email service provider will either quarantine or reject that email. However, if the email comes from [email protected], then the email service provider won’t be able to tell if the mail was sent from a legitimate source or not.
Similarly, if a password is compromised and someone hacks into your actual email server, DMARC alone won’t solve the phishing problem.
Myth #2: Setting up DMARC Automatically Protects You
DMARC is one of the most widely recognized email security protocols worldwide, to the tune of billions of email addresses that support it. So when you create a DMARC record, not only is it a commonly accepted strategy, but it should protect you, right?
The truth is that setting up a DMARC record is only part of the equation. Although it gives email recipients the information they need to verify your domain, it doesn’t get you all the way to the finish line. to gain the protection of a DMARC strategy, you need to specify what you want to do with any emails that don’t pass muster. So if you want questionable emails to be quarantined or rejected, you’ll need to make sure your record indicates this. A staggering majority of brands that employ DMARC don’t set up a policy for what to do with those emails. So they are not protected as well as they could be by updating this setting.
Myth #3: You Only Need DMARC if You Send Emails From Your Domain
It’s easy to see why you might think this. After all, if you’re not sending emails from a domain, you don’t need to worry about whether you’re being impersonated, right?
The hard truth is that hackers can spoof any domain, regardless of if it’s being used to send emails. So to truly protect your brand, you need to set up DMARC for all of your domains. Furthermore, if there’s a chance you ever might want to send emails from a particular domain, you will want to ensure that you’re not starting out fighting your way back from a bad domain reputation.
Myth #4: DMARC is a Great Set and Forget Solution to Email Security
You’ve got your SPF and DKIM policies configured, and your DMARC protocols are set up. Time to kick back and relax about your email security from here on out, right?
Not exactly. Realistically, that’s just the first step. Long term, you’ll need to make sure to stay up on your email security and the IP addresses your third party SaaS apps are using. Anytime you make a change to your email marketing service or you register a new domain, your DMARC policies will, at a minimum, need to be re-examined. More likely, they’ll need to be updated. Moreover, how will you monitor the data from your DMARC reports and fight back against any fraudsters that attempt to spoof your domain? That’s where a DMARC managed service like EasyDMARC is an ideal solution for your company.
Myth #5: DMARC is Easy to Implement
All you have to do to set up DMARC is to add a record to your domain DNS settings, then identify an email to send the records to, right? Well, sort of. Although correct , unfortunately, the reality is that it’s not so simple unless you really know what you’re doing.
Truthfully, that’s the beauty of a managed DMARC service like EasyDMARC. They make it easy for brands because we manage the headache for you. After all, not only can the reports be tough to understand, but it’s not always easy to compare IP addresses with the individuals sending legitimate emails from your domain. You likely don’t realize how intricate your email system is. Especially if you have multiple domains and SaaS integrations, and potentially more than one email service provider.
Furthermore, when you set up your SPF and DKIM protocols, you’ll need to factor all of this information, as well as the associated IP addresses, to implement everything successfully.
How to Add DMARC Step by Step
Step 1: Configure Your SPF
DMARC requires SPF and DKIM to work, so the first place to start is by setting up your SPF. Before you get started, you’ll want to make sure you know your IP address.
Then, open your DNS settings and create a new txt record:
v=spf1 a mx ip4:xxx.xxx.xxx.xxx -all
Save the settings. It may take an hour for the settings to take effect.
From there, you’ll want to check your SPF record in your DNS to make sure that it’s set up correctly.
Step 2: Configure Your DKIM
When you use an external email service, they may have a feature to help you set up DKIM. Follow their steps, and then as part of their domain authentication protocol, they may give you some additional DNS records. Just like when you set up SPF, add a new txt record for each key they give you, and publish them following their directions. You’ll need to do this for every 3rd party you use to send emails.
Once again, it may take an hour to take effect, so check to confirm they’re set up properly before moving forward.
Step 3: Publish Your DMARC Record
You’ve already set up SPF and DKIM, so now you’re ready to configure your DMARC. Go back to your DNS settings, and create a new txt record.
For the value, you’ll want to use:
“v=DMARC1; p=none; rua=mailto:[email protected]”
The value for v will never change; it should always be DMARC1.
The value for p is what you want email servers to do with emails that don’t pass your DMARC protocol.
- p=none no action to be taken
- p=quarantine (or to send to spam)
- p=reject completely
To fully protect your domain, you’ll want to set either q or r. However, if you are just starting out, you may be better served to choose none until you verify that everything is working properly.
The value for RUA is the email address where you want to receive reports about your email performance.
Once you’ve built the record, click publish. Again, you may need to wait an hour for the settings to take effect.
Step 4: Review the Reports to Confirm Settings
Now wait for the DMARC reports to start rolling in and start checking them out to gauge your email performance.
As we mentioned above, understanding the reports isn’t always easy. That’s where it may be helpful to employ a managed DMARC service like EasyDMARC as an extension of your team. We will put the highly technical report into a format you can easily understand. We’ll take care of all the hairy details for you too, making it a truly painless effort for you!
Step 5: Monitor Your Emails
Check to ensure that all of your emails are authentic and reaching their target audience. Be sure to monitor to confirm that your SPF and DKIM settings are correct. If you’re finding errors, go back in and make sure that they are configured correctly in your DNS.
If you think you’ll need help with this, it’s a good idea to work with a managed solution like EasyDMARC from the get-go. We’ll help guide you into what needs fixing and adjusting. In fact, with less than 20 minutes, we can move your email protection into the strong range.
Once your email settings appear to be working correctly for a few months, it’s a good time to update your DMARC record to the quarantine setting (“q”). And, once again, after that’s working properly for several months, you can update this setting to reject (“r”).
The reason you’ll want to take a tiered approach to adjust this setting is to make sure that no emails are falsely marked as legitimate and vice versa.
Step 6: Continued Monitoring
Although your set up is complete, DMARC isn’t a set it and forget it solution. It’s important to keep monitoring your emails and your reports to make sure that everything is working properly. Moreover, as your organization grows and changes or starts working with new email providers, you’ll need to revisit your settings to ensure optimal email delivery.
Other Considerations You Should Make Regarding DMARC
Just as you must set up DNS records as you configure your SPF and DKIM records, you must also have reverse DNS records. This ultimately gives email service providers a way to compare your IP address to your hostname, making them less likely to block your email.
Check out easyDMARC pricing.
The Bottom Line
Employing DMARC protocols is an absolute must to stay ahead today as a brand. Beyond that, you must take the time to do it the right way. Anything less potentially means less consumer trust, fewer delivered emails, and a spoofed domain that damages your brand and your clients’ security.
However, as busy as you and your team are, adding “one more thing” to your to-do list can be tough to stomach, so when you need to find a way to understand reports that aren’t in plain English. If this sounds like you, then working with a service like EasyDMARC is the perfect solution to help prevent phishing and fraud while maintaining your clients’ trust and your brand’s reputation.